Denial of Service using Cookie Bombing
Hello Guys! This is my first write up, I hope it would be informative. This article is about bug, i recently found on the private program on Hackerone. As this was found on the private program, i would mention it as example.com site throughout this article.
Let’s start..! While starting bug hunting on any website first thing i do is load the main page of the website on the browser and observe which technologies being used by website through browser extension Wappalyzer. As usual, i loaded home page of the example.com on the browser and started observing requests though Burp proxy.
While observing headers and response of the first request which was simple GET request to homepage WWW.EXAMPLE.COM, it came to my mind that why not check hidden get parameters?
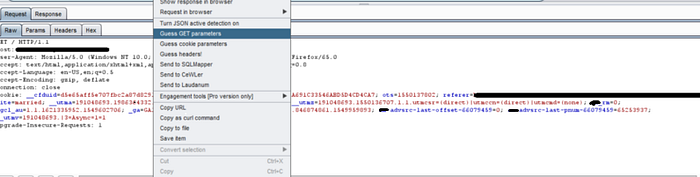
As per above Image, I started brute forcing parameters using Burp extension Param Miner. It identified few parameters as per below image.
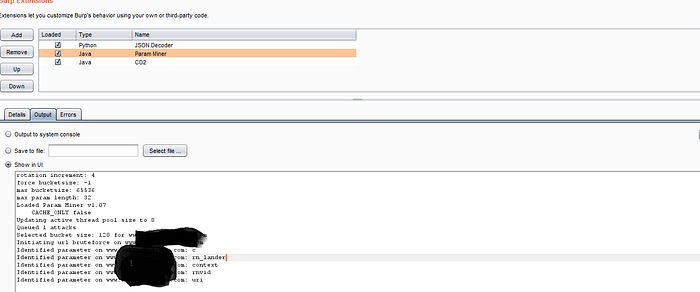
I started firing requests with the above identified GET parameters with twisted inputs. Upon observing response from the server, I observed that using these GET parameters one can set the cookie values as input applied to these parameters was set as a cookie value on the response.
So input values to those GET parameters was allowing to set cookie values. I started thinking is there any way to exploit this behavior? I started doing google about vulnerabilities possible using this behavior. I never heard or aware about cookie Bombing technique until I get the link of below article written by filedescriptor.
I though to try denial of service using cookie bomb method as explained by him on above blog.
Idea behind this technique was that most servers rejects the request with the header of around 8 KB. Any single cookie could contain 4 KB data. So if we make victim to set two cookies with 4KB data, server would reject all the further requests from the victim with the response “Request Header or Cookie too Large.”
In our website example.com, I set the get parameters context and utm_source with larger string of 4KB as per below request.
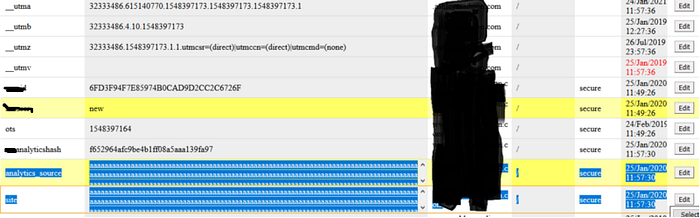
With above request cookies analytics_source and site were set with 4KB data which we supplied in the input. By default server also set the validity of the cookie one year which means victim would not be able to access website using same browser for one year period or victim has to manually delete cookie from the browser.
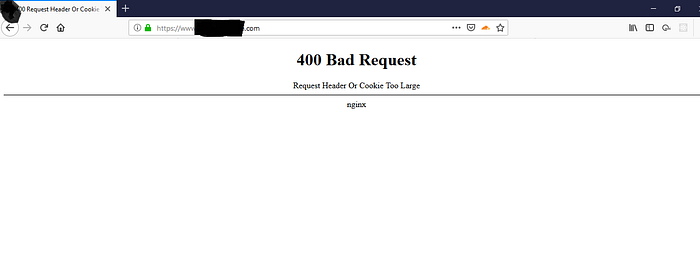
As seen above, server would reject all the requests from the victim browser now till one year or victim would delete cookies from browser.
With above findings and POC, I submitted bug to the program and rewarded me with the $350 bounty .
